
Delving into the World of Eavesdropping Techniques
In today’s digitally-driven age, eavesdropping has become a buzzword in various circles. It’s a skill that has evolved with technology, allowing individuals to gather valuable information discreetly. Whether you’re a cybersecurity enthusiast, a curious mind, or someone concerned about their own privacy, understanding the intricacies of eavesdropping is essential. In this article, we’ll explore this intriguing subject, providing insights into its methods, implications, and preventive measures.
Eavesdropping: What Is It?
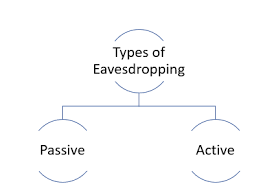
Eavesdropping, in its essence, involves the unauthorized interception of private conversations or communications between individuals. It can occur in various forms, such as wiretapping phone calls, monitoring online chats, or even discreetly listening to conversations in person. While eavesdropping can serve legitimate purposes in security and intelligence, it often raises ethical concerns when used for personal gain or malicious intent.
The Evolution of Eavesdropping Techniques
1. Traditional Eavesdropping
Before the digital era, Its primarily involved physical surveillance. This included techniques like wiretapping, hidden microphones, and covert listening devices. In espionage and law enforcement, these methods were essential for gathering crucial information.
2. Digital Eavesdropping
With the advent of the internet and smartphones, It has evolved significantly. Cybercriminals have harnessed technology to intercept emails, monitor social media accounts, and compromise personal information. This is a pervasive threat in today’s interconnected world.
The Implications of Eavesdropping
It can have far-reaching consequences, both for individuals and organizations. Here are some key implications:
1. Privacy Breach
When your conversations are intercepted without consent, your privacy is violated. This can lead to feelings of insecurity and distrust.
2. Information Theft
Eavesdroppers can steal sensitive information, such as financial data or trade secrets, leading to financial loss and reputational damage.
3. Legal Ramifications
In many jurisdictions, It is illegal unless conducted by law enforcement with proper authorization. .
Protecting Yourself from Eavesdropping
1. Encryption
Utilize end-to-end encryption for your digital communications to ensure that only the intended recipient can decipher your messages.
2. Regular Security Audits
Regularly assess your digital devices and networks for vulnerabilities. Update your software and use strong, unique passwords.
3. Be Vigilant
In physical settings, be cautious of your surroundings. Avoid discussing sensitive matters in public places where this attack may occur.
Transitioning into a Secure Future
In conclusion, understanding the world of eavesdropping is crucial in safeguarding your privacy and sensitive information. Whether you’re an individual seeking to protect your personal conversations or an organization defending against cyber threats, being informed is the first step towards security. By following preventive measures and staying vigilant, you can navigate the digital landscape with confidence, knowing that your information is secure.
Remember, the digital world may be evolving, but so are the methods of eavesdropping. Stay one step ahead, and keep your conversations confidential in an ever-connected society.